Category: Security

Society Isn’t Ready for AI Deepfakes | Are You? How Spoofed Communications Put Everyone at Risk
Society Isn’t Ready for AI Deepfakes AI deepfakes are no longer limited to viral videos or fake images online. Today, artificial intelligence can replicate a person’s face, voice, and mannerisms in real time. AI can do it well enough to be used in phone calls, video chats like FaceTime or Teams, and other live interactions where people assume what they see […]
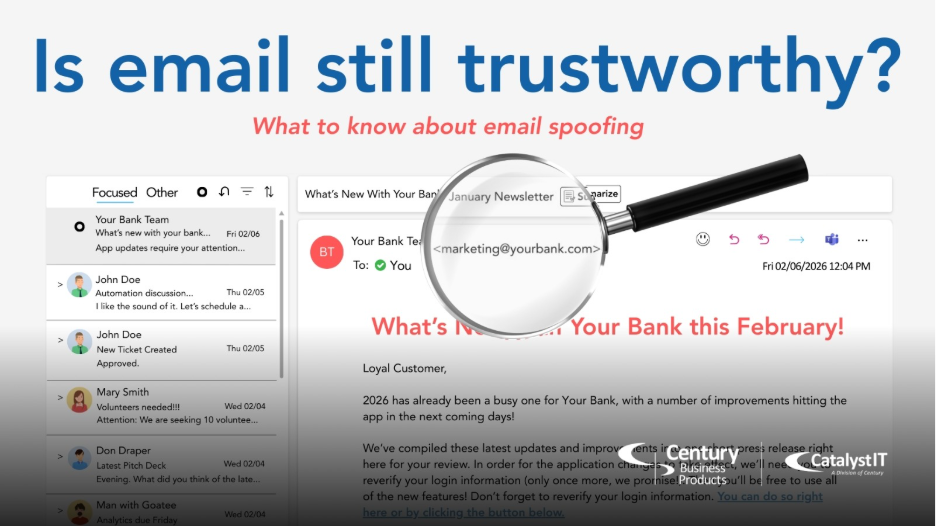
Is Email Still Trustworthy? What to know about Email Spoofing
Your inbox might be lying to you. And cybercriminals are hoping you won’t notice. Most people think email works like Caller ID. If you recognize the phone number, you can trust the caller. That is a dangerous misconception. Imagine receiving an urgent email from your boss and frantically following their instructions… only to find out later that the email didn’t actually come from your boss, even though the “from” address was correct. That’s the very real threat of Email Spoofing. You cannot trust an email simply because you recognize […]

Zero Trust Security: The Mindset Every Business Needs
If a stranger knocked on your door, would you let them walk into your house without verifying who they are? Of course not. Yet that’s exactly how many businesses treat their digital environments by trusting users, devices, and applications without confirming who they are or what they’re doing. Trust is a privilege and a vulnerability. […]
Anatomy of a Phish: The Psychology Behind Phishing
Much like the Academy Award winning film, Anatomy of a Fall, phishing has everything to do with psychology. Cybersecurity threats aren’t always about complex code or brute-force attacks. Often, the most dangerous breaches start with a simple conversation, a convincing email, or a familiar voice. This is the essence of social engineering—a tactic that manipulates […]
Windows 10 End of Support Guide
It’s fair to say Microsoft has a complicated relationship with Windows 10. Following the less-than-stellar reception of Windows 8, Windows 10 arrived as a beloved successor. Its ease of use and familiarity cemented its popularity. However, that very popularity has created a hurdle, with many users hesitant to embrace the newest operating system (OS), Windows […]
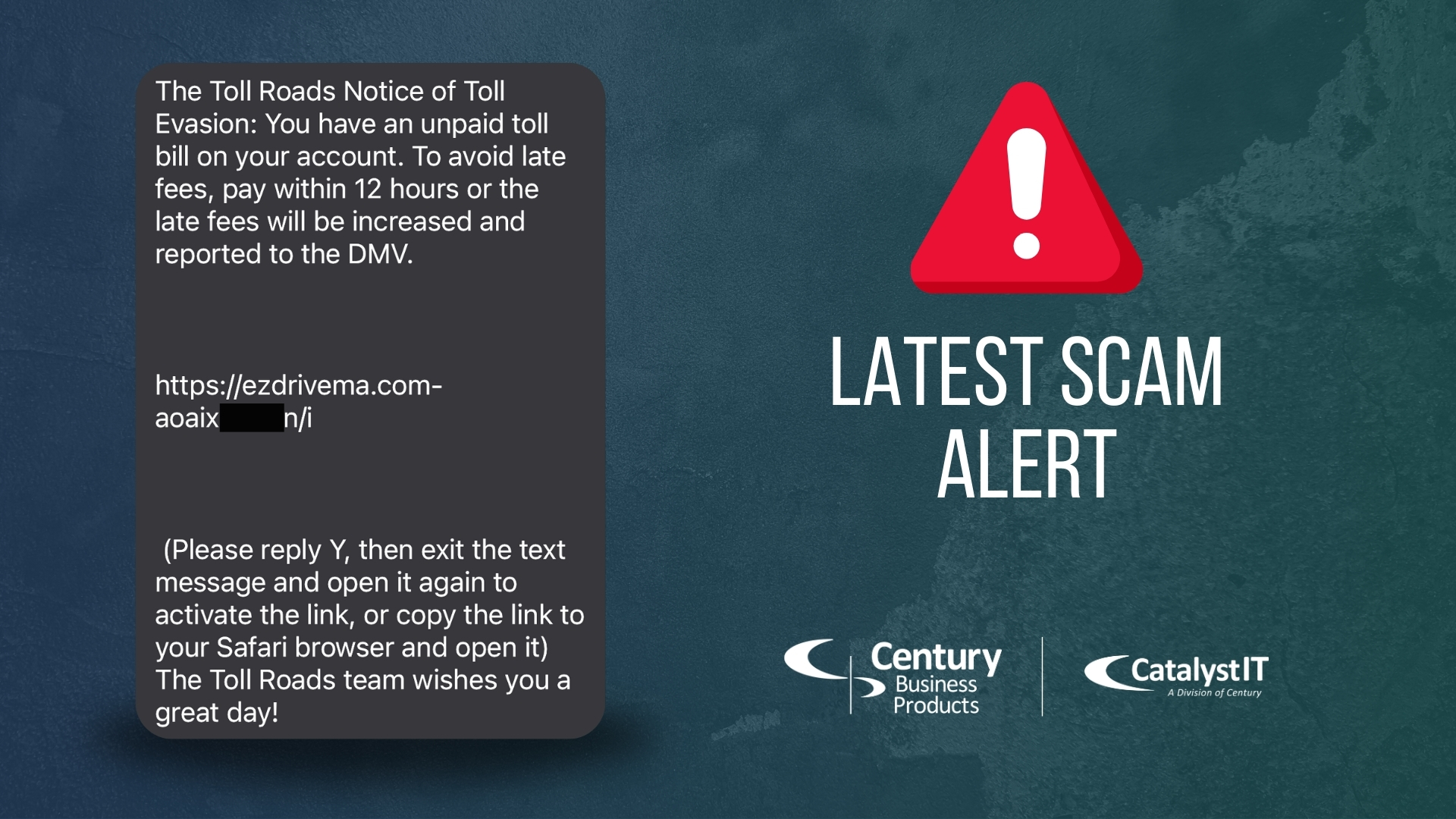
The Latest Text Message Smishing Scam – Toll Evasion
Be aware of the latest nation-wide text messaging scam Have you received a text that looks like either of these? These are fraudulent attempts to lure you into divulging person information or downloading malicious viruses. Smishing This type of texting scam is called Smishing, also known as SMS Phishing. Similar to the Phishing emails that you’ve probably […]

Minimizing Third-Party Risks in a Connected World
From supply chain partners to software providers, relying on third-party vendors is essential. These relationships drive our operations. However, every external connection introduces potential risks. Supply chain attacks are no longer a rare occurrence. Cybercriminals actively target vulnerabilities within these complex networks, putting businesses of all sizes at risk. Data breaches, service disruptions, and reputational damage are […]

What did we learn from the CDK and CrowdStrike Incidents?
A massive data breach rendering thousands of car dealerships offline and a flawed update crashing millions of Windows systems around the globe… just 31 days apart. The damage amounted to over $6 billion in financial losses for the affected businesses. With several months between now and then, what have we learned from the CDK and CrowdStrike […]
Five Simple Ways to Self-Assess Your Cybersecurity Risk
The holidays inch closer and our to-do list piles up. During the busy season of year-end budgets, new year planning, and gift shopping for family and friends, some chores invariably fall behind. Perhaps you haven’t cleaned your desk, watched that webinar, or started that project you’re procrastinating. All of those are fine to put off […]
Seven Common Phishing Scams: Understand and Prevent Attacks
Imagine starting your day with a cup of coffee, ready to tackle your to-do list, when an email that appears to be from a trusted partner lands in your inbox. It looks legitimate, but hidden within is a phishing trap set by cybercriminals. This scenario is becoming all too common for businesses, both big and small. Phishing scams are […]